These days one need not go far to find a plethora of new cloud or cloud-enabling platforms and tools – flying under the banner of ‘DevOps’ something or other. You see, as it turns out, software did end up eating the world, and now most companies are in some sense software businesses – whether they know it (admit it) or not. As organizations transform digitally, an emergent need arises to do the same in the cloud infrastructure domain. Firms need to transition to strategies that favor cost variability, developer focus, and scalability over the capital, term commitments, and the bespoke solutions of yesterday. With more software being built and that software becoming ever more business-critical, development must be operationalized in such a way as to allow for a more deliberate alignment and integration with the core business and it’s strategic goals.
Usually when people talk about DevOps, they’re really referring to things like cloud services and automation tools that are used to enable a DevOps software delivery process. But the challenge for most companies lies in determining what specifically does the “process” entail and where to start. Continuous this or automated that is great, but what does it mean and why is it necessary, how does it fit into organizational processes, and finally, what are the end goals for the business? The answers to these questions are largely outside the scope of this post but the point is to illustrate that merely having a little bit of context, actually seeing the “what” and the “how”, provides some valuable clarity around the tactics necessary to start down the path of an effective cloud strategy.
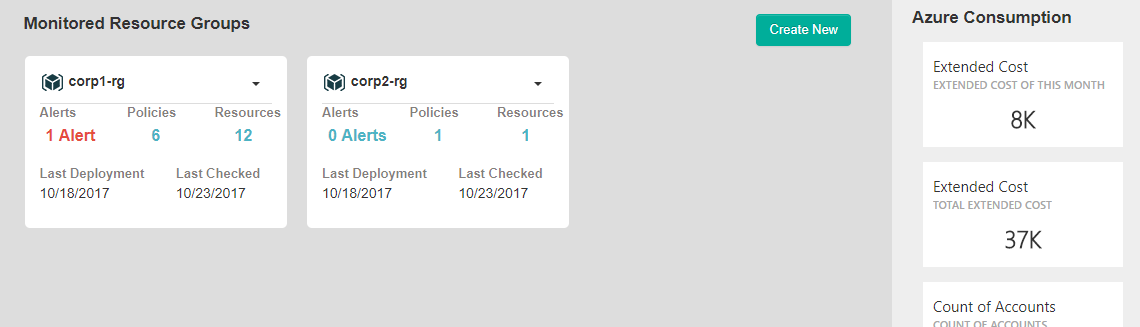
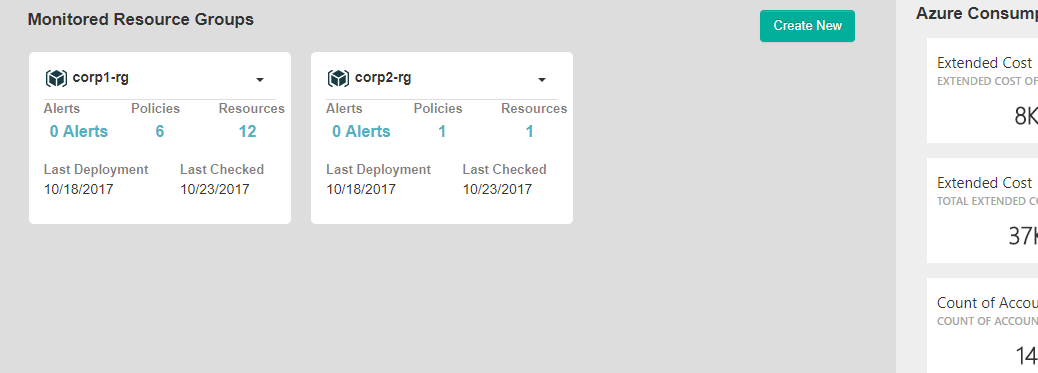
This post serves to provide some of that additional context around DevOps, continuous operations, and security. In short, we think a real world example may help! We’ll show you an example of how companies are using our software, OpsCompass Helm, to automate critical IT operations and security functions, making the move to the cloud quicker and safer. The following example is a simple but common scenario in enterprise Azure environments.
Guardrails, not gates
In modern cloud scenarios, developers are deploying code frequently and often times as part of an automated CI/CD pipeline. Cloud operations is charged with both ensuring full-stack availability, performance, and security as well as enabling the frictionless and frequent deployments that characterize the DevOps process and define the cloud advantage. Traditional process gates aren’t effective in this agile environment so other, more automated and better integrated, methods are needed to better protect these ever-changing application environments.
Scenario: The development team deployed new code to a production Resource Group in Azure. The deployment was successful and the IT team approved key changes. At a point in the process a member of the dev team had to open up a port for remote access in order to troubleshoot a minor connectivity problem. OpsCompass Helm is running in the environment and integral to the process of handling operational compliance and security in the environment.
In addition to frequent Azure tenant wide checks, Helm automatically runs a comprehensive check anytime a new deployment happens. This allows IT ops to continuously inspect and evaluate configurations, IAM, Azure Security Center output, and policy adherence without effort or Azure expertise.
Remediation without needing the expertise
In this process, IT ops personnel get real-time alerts for high-risk changes policy breaches. Development’s deployment was successful, producing only minor alerts that were intentional configuration changes. The IT team instantly gets the alert post-deployment and can approve the changes which automatically update the known approved configuration.
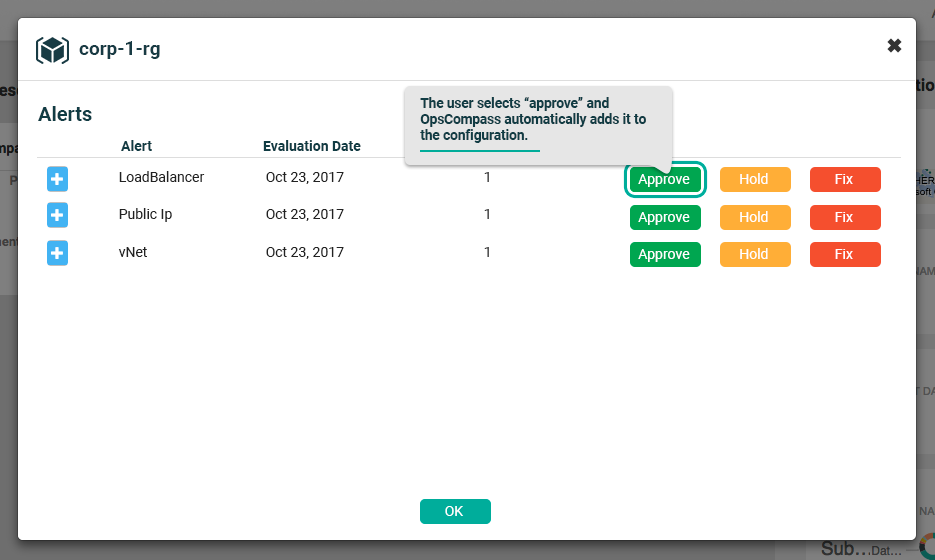
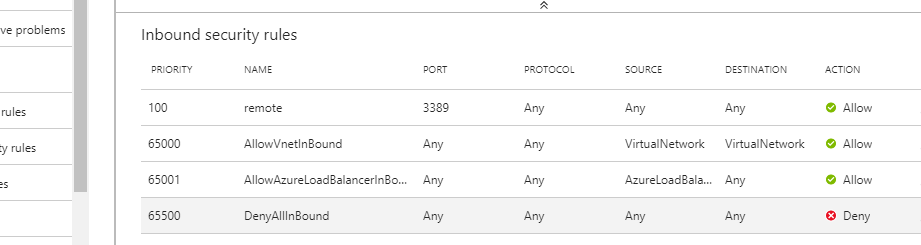
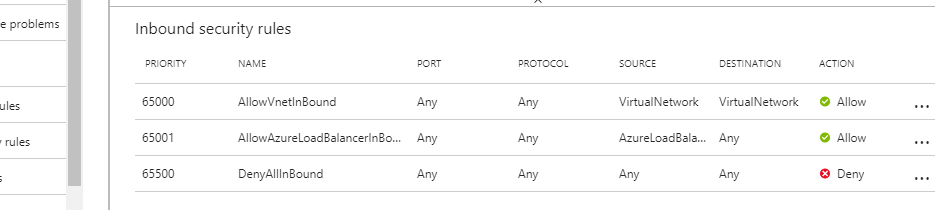
Shortly after the deployment, however, a new alert appeared. Apparently port 3389 was opened for troubleshooting but the engineer forgot to remove the Network Security Group rule, thus leaving public access open to an app server.
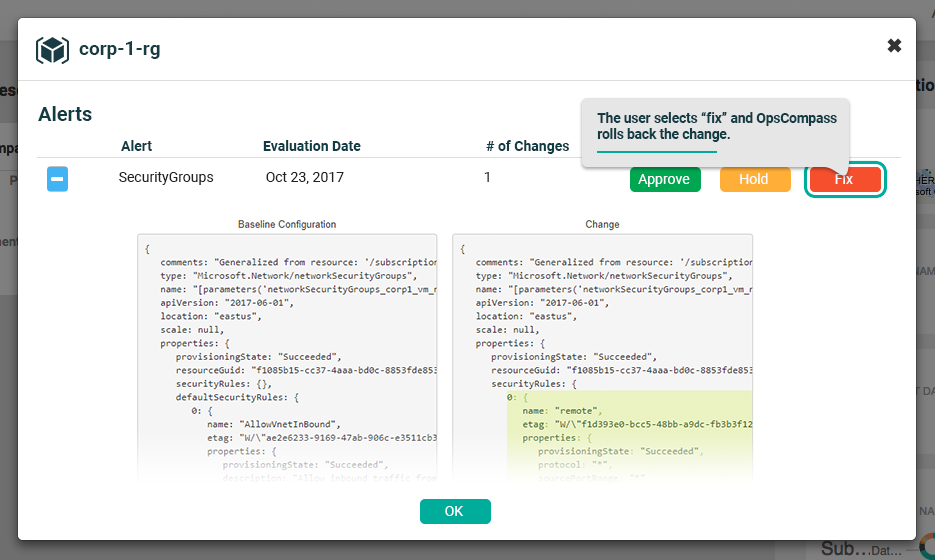
The IT ops user, who has limited Azure experience, is able to immediately see the alert and actually remediate (close the port!) the issue without anything more than a click.
Safe, automated deployments
In this example the development team has an agile process for deployments while IT is always plugged in by getting real time information about high-risk changes. With little to no Azure experience, only general IT knowledge and awareness of internal policy, staff can update known-safe-configurations or even remediate complex configuration changes. The process is fluid, integrated, and is a simple step in a more automated and streamlined cloud strategy.
Conclusion
In short, the evolution to cloud has become a deliberate strategy to align organizations around Azure and other public infrastructure providers. This transition coupled with OpsCompass Helm reduces anxiety for both Azure experts and those still building expertise – providing guardrails to this now deliberate process.





